Many websites are switching to HTTPS, a secure website. Including us! You can see in your URL bar, that our website address now has a small padlock. This indicates that all the communications between you and our server is encrypted and much harder, or impossible, to view what is being sent and received.
How TLS/SSL/HTTPS works
Transport Layer Security (TLS) and its predecessor, Secure Sockets Layer (SSL), both frequently referred to as “SSL”, are cryptographic protocols that provide communications security over a computer network. It’s a mathematical system for ensuring two computers can communicate in secret.
There are hundreds of videos and explanations online, one of the best can be found here;
Public Key Cryptography – explained by mixing coloured paints
If you’re unable to watch the video, consider it like this:
- You and I pick a base colour; lets say blue ●.
There’s no problem with this being known to anyone else. Paint it on a postcard, and tell the world! - We then each pick a secret colour of our own, and mix that with the base colour.
Perhaps I’ve chosen yellow ● and have made a green mix ●.
You have chosen red ● and have made a brown mix ●. - This is the clever part – We can then send the mix we’ve each made, to each other, publicly.
No-one can remove the base ‘blue’ paint to see what colours we chose.
This applies to bother of us too! We cannot remove colours, and we don’t have to. Our secret colour is still completely secret. - We now take each others’ mix, and mix it with our own private colour.
You now have the green mix ● I sent you (a mix of the base blue ●, and my secret yellow ●) – adding your private red ●, and we end up with a mess ●.
I have a mix the brown mix ● you sent me (a mix of the base blue ●, and your secret red ●) – by adding my private yellow ● – I have made an identical mess ●. - Result
We have not revealed to anyone else publicly the secret colour we each chose, or the final mix.
Only we know our personal private colour, but we also both share a secret colour too.
We both have the same final mix, and this can be used for further encryption.
The key point is that there is no need for you or I to ‘unmix’ the paint, that would be very difficult – but it is what an attacker would need to do.
Neither of us, nor anyone else knows what our secret colours were either. Private keys and colours should never be shared.
This is exactly the same system used in private key cryptography. There is a private key we each create, and a shared ‘public’ key that we mix with. The keys are large prime numbers, and the mix is a complex mathematical operation – but the logic is exactly the same.
What’s changed, and why is HTTPS now popular?
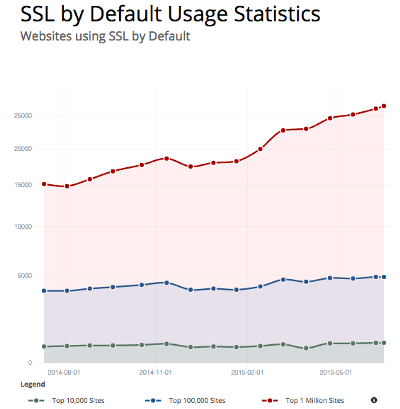
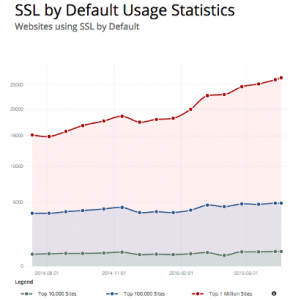
Interest in HTTPS, SSL has grown in popularity in the last four years and is set to increase again as more sites are taking to securing their sites.
As always, there are a whole host of reasons;
- In August 2013, following the Snowden leaks, new details about the NSA’s data mining activity were revealed. Reportedly, the majority of emails into or out of the United States are captured at “selected communications links” and automatically analysed for keywords or other “selectors”.
- Many users are now using public networks, not just libraries and internet cafés, but public Wifi access points – often unencrypted themselves; allowing other users’ to potentially spy on them.
Back when Facebook/Twitter didn’t use encryption, it was possible to take over a users session remotely in these environments, without the user knowing. One of the most popular methods was a simple browser extension called FireSheep – meaning almost anyone could do it. - Users and companies are more interested in privacy. Alongside governments, workplaces and ISPs have been known to monitor web traffic. HTTPS has commonly been used by banks and financial institutions and it’s now recognised that users’ data can be as valuable and should at least be treated as such.
- In 2014, Google announced HTTPS will be a factor in its ranking. It’s not yet clear whether this is treated as a reward, or penalised for insecure websites; but for marketing can often be a quick win for both SEO and for user trust. Already Firefox alerts users using a username and password to login to a non-HTTPS site. Soon, browsers will mark all unsecured websites as insecure.
- For various technical reasons, acquiring a certificate was expensive and difficult. There were very few certificate authorities, and they charged a lot of money. These are now much more affordable, and in the case of Let’s Encrypt (see below), is free.
- There were also other technical issues, previously it was required that each HTTPS-encrypted website had it’s own individual IP address. Given the lack of IPv4 addresses, this was often an additional expense. That has now changed with the support of Server Name Indication (SNI) in browsers and web servers. This allows encrypted websites to be served on the shared systems with the same IP address and running on the same computer. This vastly decreased the price of hosting a secured site and opened up the use to shared hosting. This does raise compatibility issues as detailed below.
- The mathematical operations required to encrypt data were also of some concern, particularly to larger sites. With the improvements to CPU architecture, including hardware support for cryptography, this is of almost no concern now – to the point that both Facebook and Twitter force the use of encryption.
It’s highly recommended that all sites use encryption; unless they have customers or users who would be unable to use the site.
Browser Support and Compatibility
In most cases, all recent web browsers, smartphones and devices can support encryption in at least some method.
The most recent of these is for shared hosting SNI (shared IP address – Server Name Indication), as explained above. This has been integrated into most devices, with exception to Windows XP and some older devices. A list of these can be found on Wikipedia.
Before forcing an encrypted website, it should be confirmed which browsers your users are using and if so, avoid using SNI or enforcing high encryption. It is possible to avoid using SNI by using a separate IP address, and adjusting webserver settings to permit different types of encryption.
It is also possible to use very-high level encryption to ensure user data and trust.
We’re very much able to assist with this, even for older devices; please do get in contact if we can help.
Types of Certificates
There is quite a confusing array of marketing terms used when selling certificates. These vary by how much they prove the ‘legal entity’ is the one controlling the website.
From a technical standpoint, there is no difference in encryption between the three. The difference is what validation is done against the company; and how this is indicated to the user.
There are three main types of certificates which can be generated are;
Standard (Domain Validated) Certificates
A Domain Validated Certificate provides a solid encryption. The ability to use a certificate for this domain relies solely on having control over the domain. No further identification or proof is needed. This is almost always an automated system, checking against the domain name and email address on the record.
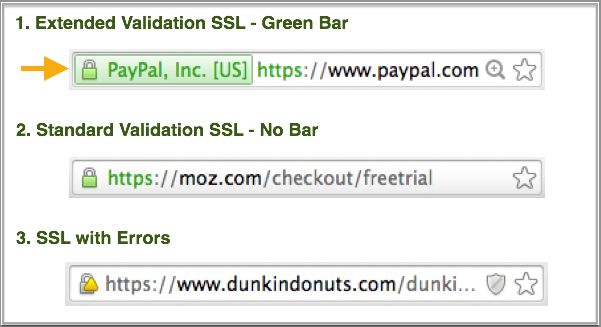
Web browsers usually indicate standard certificates with a green lock symbol in the URL bar.
Organisational Validation
Organisational Validation certificates can be issued to purchasers with the right to administratively manage the domain name. This includes checking the applicant’s business credentials (through databases including the Articles of Incorporation) and even making sure that the company’s physical address matches the application.
OV certificates appear in the browser identical to DV certificates. The site seal (more info) provided with the certificate typically includes additional information that is more trustworthy to the user; however this is typically never seen.
Extended Validation
EV certificates use the same encryption as organization validated certificates and domain validated certificates. The increase in security (and price) is due to the manual identity validation process. This is the highest level of validation, and can take a few days to complete. The process includes checking the physical location, telephone numbers, and ensuring the applicant is authorised on behalf of the company or business represented.
The guidelines are to:
- Establish the legal identity as well as the operational and physical presence of website owner.
- Establish that the applicant is the domain name owner or has exclusive control over the domain name.
- Confirm the identity and authority of the individuals acting for the website owner, and that documents pertaining to legal obligations are signed by an authorised officer.
Websites with EV support are often indicated very differently in the browser; showing the company name who owns the certificate, a distinctive background colour in the URL bar, and a lock symbol.
Domain Features
Other commonly confused features include;
- Multidomain Certificate – this can apply to any certificate type, and simply allows multiple domains within the same certificate. These are just the same but include other domains which have also been validated. It is commonly used for www. and non-www. prefixes, or for multiple TLDs. For example, within our www.frag.co.uk certificate, the ‘Certificate Subject Alt Name’ also allows use on other domains; frag.co.uk, www.frag.co.uk, frag.uk, and www.frag.uk.
- Wildcard Certificate – these are similar to Multidomain certificates, but apply to all subdomains – e.g. anything.example.com. These cannot be individually validated and require more complex DNS validation. For security reasons, these are not available to EV certificates.
Purchasing
The only options for higher-security certificates such as EV and OV are to purchase from a certificate authority or from a reseller. They will provide help and advise on can you can configure it with your hosting. Often can be purchased via your hosting provider, who can set this up for you. For standard certificates, smaller sites, especially smaller sites, there is the option of Lets Encrypt.
The prices of certificates will vary, but generally these are charged at a yearly rate, standard certificates are often very low cost (or sometimes free), and EV and OV are respectively much more expensive due to the validation process as above.
The other option available, especially for small sites, is the free certificate option in the new service, Let’s Encrypt.
Let’s Encrypt
Let’s Encrypt was set up by the Internet Security Research Group. They have set up a certificate authority providing basic certificates, for free, in order to make “encrypted connections to World Wide Web servers ubiquitous”. This works in a very different way to most authorities and resellers; Certificates are completely free.
They also almost completely maintenance-free, too. In contrast to purchased certificated, they are only valid for three months – but they can be renewed completely automatically using a scheduled task on the server. This means that almost no human interaction is needed, other than reviewed and monitoring the update services.
Let’s Encrypt do not offer EV or OV certificates, only standard security certificates. However, they can be created with multiple domains, and are validated and renewed using CertBot and other similar API tools.
Let’s Encrypt have a huge list of new features, including wildcard certificates coming. This again, will be using their own system – not much documentation as yet, but this will need a DNS TXT record, for a dns-01 challenge using RFC 2136 Dynamic Updates. As always, if you are interested – it’s worth taking a look at their Blog post, as well as the Github source code and readme file.
Best Practice
For most sites, Let’s Encrypt is an ideal upgrade to an insecure site. It is worth considering the visitors to your site to ensure that encryption is suitable for all your users; as explained above, some clients are not able to support connections in some environments.
For larger sites, including those who store payment details themselves, or personal or very secure information, a higher-level certificate such as EV or OV is highly recommended.
If you need help or advice with certificates, please do get in contact and we’ll be happy to help.